| Vendor |

|
| Product | Piwigo |
| Affected Version(s) | 2.9.0 probably prior |
| Tested Version(s) | 2.9.0 |
| Vulnerability Discovery | May 29, 2017 |
| Vendor Notification | May 29, 2017 |
| Advisory Publication | June 2, 2017 [without technical details] |
| Vendor Acknowledgment | June 16, 2017 |
| Vendor Fix | June 14, 2017 |
| Public Disclosure | June 15, 2017 |
| Latest Modification | June 15, 2017 |
| CVE Identifier(s) | CVE-2017-9463 |
| Product Description | Piwigo is a full featured open source photo gallery for the web, built and supported by an active community of users and developers, make it easy and faster to deploy a photo gallery In just seconds. |
| Credits | Eric Castañeda, Security Researcher & Penetration Tester @wizlynx group |
| SQL Injection | |||
| Severity: Medium | CVSS Score: 4.7 | CWE-ID: CWE-89 | Status: Fixed |
| Vulnerability Description | |||
| The application Piwigo is affected by a SQL injection vulnerability affecting version 2.9.0 and possible priors. These vulnerabilities could allow remote authenticated attackers to obtain information in the context of user used by application to retrieve data from database. | |||
| CVSS Base Score | |||
| Attack Vector | Network | Scope | Changed |
| Attack Complexity | Low | Confidentiality Impact | Low |
| Privileges Required | High | Integrity Impact | Low |
| User Interaction | None | Availability Impact | Low |
The Piwigo has a Blind time based SQL injection vulnerability due to lack of input validation on user list page, being possible to retrieve information like user name and database name through SQL sentences appended to iDisplayStart parameter.
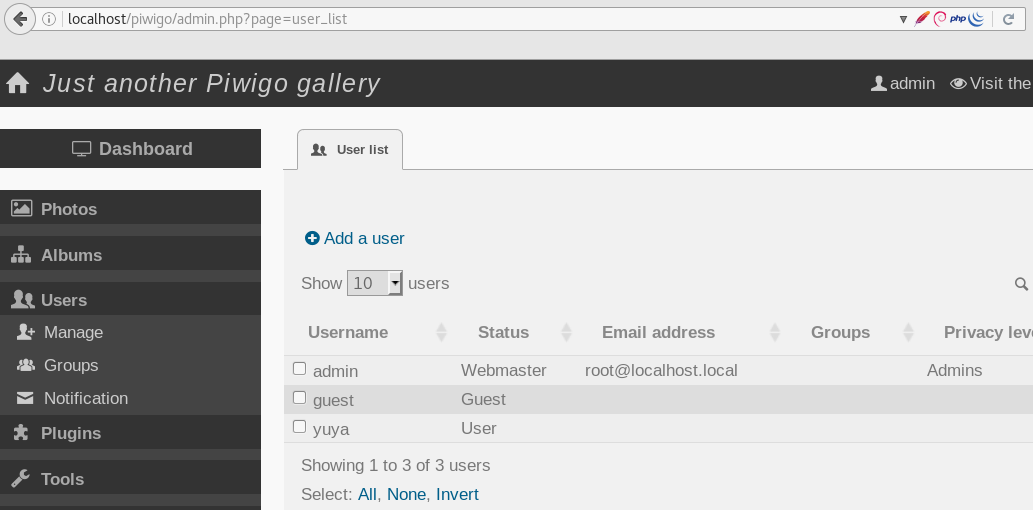
To replicate this issue an administrator level user is required. On Piwigo application we should access to User List menu and retrieve some users, this show a user list which contain username, email address and level permissions. Through this feature is possible to retrieve some information from database.
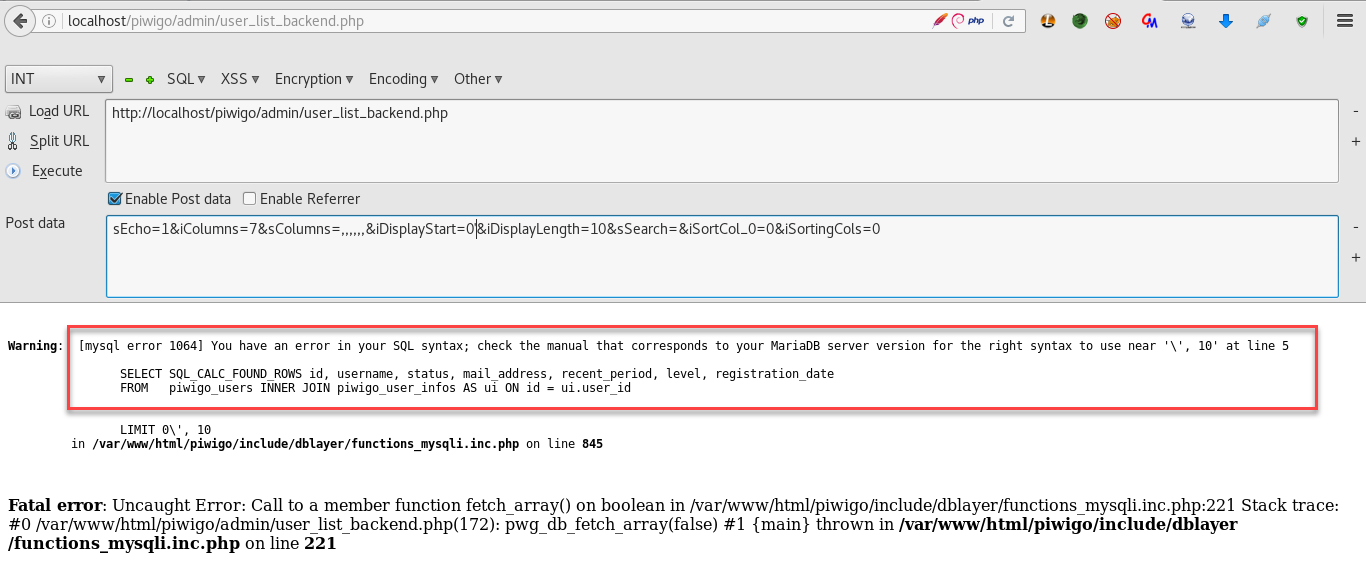
The affecter URL is http://localhost/piwigo/admin/user_list_backend.php and the following data is sent via POST request to above URL:
Some parameters are not mandatory so an alternative post data can be use instead
The content is retrieved from http://localhost/piwigo/admin/user_list_backend.php which is a webservice that return information via JSON
The following image shows a normal request and response

If a single quote is passed as value on iDisplayStart parameter a MySQL syntax error is showed.
the following screenshot shows the retrieval of the database’s name by automating the exploitation of the SQL injection via SQLmap:
